|
The Internet of Things (IoT) is no longer a futuristic concept. It's rapidly transforming industries and reshaping how businesses operate.
IoT is a blanket term to describe smart devices that are internet enabled. Example? Anything from smart sensors monitoring production lines to connected thermostats optimizing energy consumption. Experts project the number of connected devices worldwide to continue growing. It’s estimated to rise from about 15 billion in 2023 to 21 billion in 2026. IoT devices are weaving themselves into the fabric of modern business operations, but successfully deploying them on your existing network isn’t always easy. In fact, it can feel like navigating a maze. Have you been struggling with the integration of smart devices? This guide will equip you with the knowledge and steps you need. Step 1: Define Your Goals and Needs Before diving headfirst, it's crucial to have a clear vision of your goals. Ask yourself and your team a few questions, which will help ensure you’re aligning smart devices with business needs. What problem are you trying to solve with IoT? Are you aiming to improve operational efficiency? Possibly, you want to gain real-time data insights. Or you may want to enhance remote monitoring capabilities. It’s important to target your IoT device deployment. Defining the issue that it’s meant to solve helps you do that. What type of data will you be collecting? Take time to define the nature and volume of data generated by your chosen devices. This is essential for choosing the right network infrastructure. What level of security do you need? Security measures depend on the sensitivity of the data collected. You might need specific measures to protect it from unauthorized access. Go through these questions as a first step. You'll gain a clearer picture of your specific needs, enabling you to select the most appropriate IoT devices and network solutions. Step 2: Select the Right Devices and Network Infrastructure With your goals in mind, it's time to choose your components. You’ll want to look at both the devices and the infrastructure of the network. IoT Devices When choosing smart devices, consider factors like:
Network Infrastructure Your existing network might be lacking. It may not be equipped for the extra traffic and data generated by IoT devices. You may need to upgrade your bandwidth. As well as deploy separate networks for IoT devices. You may also need to invest in dedicated gateways – ones that can manage communication between devices and the cloud. Step 3: Focus on Security Throughout the Journey Security is paramount in the realm of IoT. Compromised devices can become gateways for cyberattacks. Malware attacks on IoT devices increased 77% during the first half of 2022. Here are some key security considerations: Secure the Devices Ensure the chosen devices have strong passwords. They should also be regularly updated with the latest firmware. You want to choose devices that offer features like encryption and secure boot. Secure the Devices Create separate networks for IoT devices and critical business systems. This minimizes the potential impact of a security breach on your core operations. Install Network Access Control (NAC) Install NAC solutions, such as multi-factor authentication. These controls restrict access to your network only to authorized devices. They also help you enforce security policies automatically. Track and Maintain Continuously track your network for suspicious activity. Regularly update your security protocols and software to stay ahead of evolving threats. Step 4: Deployment and Ongoing Management You should now have the necessary hardware and security measures in place. It's time to deploy your IoT devices. Here are some tips:
Step 5: Continuous Learning and Improvement The world of IoT is constantly evolving, and so should your approach. Here are some tips for continuous improvement: Analyze the Data Once your IoT devices are operational, analyze the collected data. This helps you gain insights, identify areas for improvement, and refine your strategy. Embrace Feedback Encourage feedback from stakeholders within your organization. Use it to constantly refine your implementation and address emerging challenges. Stay Informed Keep yourself updated on the latest trends and advancements in the IoT landscape. This empowers you to adapt and leverage new technologies as they emerge. Successfully deploying IoT on your business network requires careful planning. As well as prioritization of security and a commitment to continuous improvement. Get Expert Help for Your Network Devices Need help embracing a proactive approach to IoT adoption? We can help you transform your business operations. As well as unlock the full potential of smart devices at your business. Contact us today at 256-401-7072 or email us at ContactUs@CyberProtex.com to schedule a chat. Article used with permission from The Technology Press.
0 Comments
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside – cloud waste.
Cloud waste is the unnecessary spending of resources and money on cloud services. These services are often not fully utilized or optimized. About 32% of cloud spending is wasted. This can lead to budget concerns as spending skyrockets. But that figure also holds opportunity. It means that you can reduce nearly a third of cloud spending by optimizing how you use cloud tools. So, how can you reduce cloud waste at your business and save money? Here are some smart tactics to consider. Conduct a Comprehensive Cloud Audit Before implementing any cost-cutting strategies, conduct an audit. It's essential to have a clear understanding of your current cloud usage. Conducting a comprehensive cloud audit allows you to identify:
Put in Place Right-Sizing Strategies Right-sizing involves matching your cloud resources to the actual demands of your workloads. Many businesses fall into the trap of overprovisioning. This means securing more user licenses or features than they need, leading to increased costs and unnecessary waste. Analyze your workload requirements and resize instances accordingly. Use tools provided by your cloud service provider, which can identify and adjust the capacity of instances. This ensures that you only pay for the resources you truly need. Use Reserved Instances and Savings Plans Cloud providers offer cost-saving options like Reserved Instances (RIs) and Savings Plans. These allow businesses to commit to a specific amount of usage. This is in exchange for discounted rates. By leveraging these options, you can significantly reduce your cloud costs over time. Carefully analyze your workload and usage patterns, then determine the most cost-effective reserved capacity or savings plan. Find a plan that aligns with your business's long-term goals. Install Automated Scaling Policies Dynamic workloads have a need for dynamic resource allocation. Install automated scaling policies. These ensure that your infrastructure scales up or down based on demand and optimizes performance. It also prevents overprovisioning during periods of low activity. Cloud services enable you to set predefined policies for scaling. Examples are AWS Auto Scaling and Autoscale in Azure. These features help ensure efficient resource utilization without manual intervention. Track and Optimize Storage Storage costs can accumulate quickly. This is especially true when data is not regularly reviewed and archived. Estimate your storage needs, then put in place lifecycle policies to automatically downsize lesser-used data. This includes transitioning less frequently accessed data to lower-cost storage options. Regularly review and delete unnecessary data to free up storage space. Adopt a proactive approach to storage management. This can help you significantly reduce costs associated with data storage. Schedule Your Cloud Resources Schedule your cloud resources to run only when you need them. For example, turn off development, testing, or staging environments during nights and weekends. Or scale down your production environment during off-peak hours. Use available tools to automate the scheduling of your cloud resources. Base this on automated rules and policies that you define. Delete Unused or Orphaned Cloud Resources Sometimes, you may forget or neglect to delete cloud resources. Resources that you no longer need or use. This can include:
Weed Out Duplicate Services Different departments in the same organization may be using duplicate services. Marketing may use one task management app, while Sales uses a different one. Centralize cloud resources and remove duplicate tools. Having everyone use the same cloud tool for the same function can save money, as well as enhance collaboration, reporting, and data integration. Embrace Serverless Architecture Serverless computing allows businesses to run applications without managing the underlying infrastructure. You pay only for the actual compute resources used for your processes. This eliminates the need for provisioning and maintaining servers. Which reduces both operational complexity and costs. Consider migrating suitable workloads to a serverless model. This can help you optimize resource use and cut cloud waste. Schedule a Cloud Optimization Assessment Today! By following these smart tactics, you can reduce cloud waste at your business, optimize your cloud spending, and help you SAVE MONEY. You can also improve operational efficiency and environmental sustainability. Are you struggling with expanding cloud costs? Need help identifying and removing cloud waste? Our team of cloud experts can help you. Contact us today at 256-401-7072 or email us at ContactUs@CyberProtex.com to schedule a chat. Article used with permission from The Technology Press. Staying ahead in business often means embracing cutting-edge technologies. New tools can unlock new avenues for growth, especially for small businesses. SMBs are often looking for affordable ways to gain a competitive advantage. One such transformative force is Generative Artificial Intelligence (GenAI).
GenAI is a technology that goes beyond automation and the AI we used to know. It can create content, solutions, and possibilities before unimaginable. It’s so revolutionary that it’s hard to go online without seeing it everywhere. Do you have a small business seeking to grow? Looking for innovative ways to navigate the competitive landscape? Generative AI can be a powerful ally! It can drive creativity, efficiency, and growth. Let’s look at how small businesses are harnessing the potential of Generative AI. Using it to elevate their marketing strategies, streamline operations, and foster innovation. The Rise of Generative AI in Small Business Marketing The landscape of small business marketing is evolving rapidly, and the integration of AI technologies is reshaping strategies for growth. Thus, small businesses are turning to GenAI to enhance their marketing efforts. This is one example of how they are leveraging it to improve profitability. 60% of SMBs say attracting new customers is their biggest challenge, while 30% say it’s marketing to prospective clients. Not surprisingly, 74% expressed interest in using AI to help. 91% of surveyed SMBs say AI has made their business more successful. This advanced form of AI enables businesses to generate things like:
How Are Small Businesses Using GenAI? 1. Image & Content Creation and Personalization Generative AI is revolutionizing image and content creation by automating the generation of diverse and engaging visuals. Using text prompts, you can generate countless image styles and create photos and graphics that resonate with target audiences. Small businesses can also leverage GenAI to personalize marketing messages, improving customer engagement and building stronger connections. 2. Enhanced Customer Experience Small businesses strive to differentiate themselves through exceptional customer experiences, and Generative AI can play a pivotal role. AI-powered chatbots and virtual assistants provide instant responses. They offer a seamless and efficient communication channel, enhancing customer satisfaction. It also frees up staff to focus on strategic aspects of relationship management. 3. Data Analysis and Decision-Making Generative AI excels at analyzing vast datasets, as well as extracting insights and informing data-driven decision-making. Small businesses can harness the power of AI algorithms, which can help them understand market trends, customer behaviors and competitive landscapes. This data-driven approach enables more informed marketing strategies. It also helps business owners optimize resource allocation, as well as maximize the impact of marketing campaigns. 4. Innovative Product Development The creative capabilities of GenAI also extend to product development. Businesses can use AI to generate innovative ideas and concepts, including designing new products and refining existing ones. AI-driven tools provide a unique perspective. One that can spark creativity, as well as set small businesses on a path of continuous innovation. 5. Efficient Social Media Management Social media has become a cornerstone of small business marketing, and Generative AI can help to streamline social media management. AI tools can analyze social media trends, schedule posts for optimal engagement, and even generate relevant hashtags and captions. This automation allows small businesses to maintain a consistent social media presence. Empowering Small Businesses for Future Growth Generative AI stands at the forefront of technological innovation. It offers small businesses a gateway to enhance creativity, efficiency, and growth. Those who harness the power of AI will gain a competitive edge. It can especially help smaller companies reach new heights of success... and do so affordably. Small businesses that embrace GenAI can streamline their operations and marketing. They can also foster a culture of innovation that propels them into the future. We’re now in a world where adaptability is key. GenAI provides small businesses with the tools to keep pace with industry changes. It also gives them the power to lead the way. The growth potential unlocked by Generative AI extends beyond marketing. It permeates every aspect of business operations. This paves the way for a future where small businesses thrive. Well, the ones that capitalize on the innovation and strategic advantage, that is. Get Expert Guidance to Keep Your SMB Technologically Competitive Things have always moved fast in the digital world. But GenAI seems to have accelerated that even more. Don’t let your small business get left behind. CyberProtex's team of technology experts can help you take a look at your current business needs, as well as how your technology is meeting them. Next, we’ll explore ways that newer solutions can cut costs and improve efficiency. Contact us today at 256-401-7072 or email us at ContactUs@CyberProtex.com to schedule a chat. Article used with permission from The Technology Press. Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal. Especially when it comes to safeguarding sensitive information and digital assets. As cyber threats evolve in complexity, AI has emerged as a formidable ally. It empowers organizations with advanced tools and techniques. Helping them to stay one step ahead of malicious actors.
In this exploration, we delve into cutting-edge AI trends. The trends that are reshaping the cybersecurity realm, as well as fortifying defenses against an ever-expanding array of cyber threats. The Rise of AI in Cybersecurity As cyber threats grow in sophistication, traditional measures face challenges in keeping pace. This is where AI steps in. It offers a dynamic and adaptive approach to cybersecurity. Machine learning algorithms, neural networks, and other AI technologies analyze vast datasets. They do this at unprecedented speeds and identify patterns and anomalies that might elude human detection. 58% of security professionals expect a completely new set of cyber risks in the coming years. The integration of AI in cybersecurity doesn't replace human expertise. It enhances it, allowing security professionals to focus on strategic decision-making. All while AI handles the heavy lifting of data analysis and threat detection. AI Trends Sweeping the Cybersecurity Realm 1. Predictive Threat Intelligence AI is revolutionizing threat intelligence by enabling predictive capabilities. Machine learning algorithms analyze historical data, current threats, and emerging patterns. It does this to predict potential future cyber threats. This proactive approach allows organizations to put in place preemptive measures, as well as close vulnerabilities before hackers exploit them. 2. Behavioral Analytics Traditional signature-based approaches struggle to keep up with zero-day attacks and advanced “smart phishing.” But AI-driven behavioral analytics take a different approach. They focus on understanding the normal behavior of systems and users. Deviations from these patterns trigger alerts. This helps in identifying potential threats. Identification is based on anomalous activities rather than known signatures. 3. Autonomous Security Systems The concept of autonomous security systems, empowered by AI, is gaining prominence. These systems can automatically detect, analyze, and respond to cyber threats in real-time. This minimizes response times and reduces the impact of security incidents. The ability to automate routine security tasks enhances efficiency. It also allows human experts to focus on strategic aspects of cybersecurity. 4. Explainable AI (XAI) AI plays an increasingly critical role in cybersecurity decision-making. This makes the need for transparency paramount. Explainable AI (XAI) addresses this concern. It provides insights into how AI algorithms reach specific conclusions. This enhances trust in AI-driven cybersecurity. It also helps security professionals understand the decisions made by AI systems. 5. Cloud Security Augmentation With the proliferation of cloud services, securing cloud environments has become a priority. AI is being leveraged to enhance cloud security. A few ways that it does this is by:
6. Deception Technology Deception technology involves creating decoy assets within an organization's network to mislead attackers. Companies are now integrating AI into deception technology to make decoys more convincing as well as more responsive to attackers' behavior. This helps in early threat detection. It also provides valuable insights into attacker tactics and techniques. 7. Zero Trust Architecture Zero Trust Architecture, supported by AI, challenges the traditional security model. Where systems trust entities inside and distrust entities outside the network. AI-driven continuous authentication and monitoring ensure that trust is never assumed. It dynamically adapts access privileges. It does this based on real-time assessments of user behavior and risk factors. Embracing the Future of Cybersecurity with AI As the threat landscape evolves, the incorporation of AI in cybersecurity is important. It's not just a strategic choice, it’s a necessity. These AI trends mark a paradigm shift. They are enabling organizations to build more resilient and adaptive cybersecurity frameworks. It’s important to stay informed and embrace the transformative power of AI. This helps businesses navigate the complexities of the digital landscape. And do it with confidence, fortifying defenses against emerging threats. AI stands as a beacon of innovation. It continually pushes the boundaries of what’s possible in the realm of cybersecurity. The symbiotic relationship between human expertise and AI-driven capabilities is vital. It will shape the future of data security, helping ensure a safer digital landscape for businesses and individuals alike. Schedule a Cybersecurity Upgrade Assessment How strong are your digital defenses against sophisticated threats? The bad guys are also using AI. This means more dangerous phishing and network attacks. Need some help assessing your strength? Sign up for a cybersecurity assessment and shed light on your capabilities. We can help you incorporate AI-based protection and fortify your network from attacks. Give us a call today at 256-401-7072 to schedule a chat. Article used with permission from The Technology Press. The battle against cyber threats is an ongoing challenge. Unfortunately, 2023 has proven to be a watershed year for data breaches.
Data compromises have surged to an all-time high in the U.S. This is based on data from the first 9 months of the year. Meaning that numbers will only end up higher for the year. The last data breach record was set in 2021. That year, 1,862 organizations reported data compromises. Through September of 2023, that number was already over 2,100. In Q3 of 2023, the top data compromises were:
This data underscores the relentless efforts of cybercriminals to exploit vulnerabilities. As well as access sensitive information. Let’s take a look at the main drivers of this increase and the urgent need for enhanced cybersecurity measures. 1. The Size of the Surge The numbers are staggering. Data breaches in 2023 have reached unprecedented levels. They've increased significantly compared to previous years. The scale and frequency of these incidents is concerning. They emphasize the evolving sophistication of cyber threats, as well as the challenges organizations face in safeguarding their digital assets. 2. Healthcare Sector Under Siege One of the most disturbing trends is the escalating number of breaches in healthcare. Healthcare organizations are the custodians of highly sensitive patient information. As a result, they’ve become prime targets for cybercriminals. The breaches jeopardize patient privacy. They also pose serious risks to the integrity of medical record, creat a ripple effect that can have long-lasting consequences. 3. Ransomware Reigns Supreme Ransomware attacks continue to dominate the cybersecurity landscape. Cybercriminals are not merely after data. They are wielding the threat of encrypting valuable information, then demanding ransom payments for its release. The sophistication of ransomware attacks has increased, and threat actors are employing advanced tactics to infiltrate networks and encrypt data. They are also using many different methods to extort organizations for financial gain. 4. Supply Chain Vulnerabilities Exposed Modern business ecosystems have an interconnected nature. This has made supply chains a focal point for cyberattacks. The compromise of a single entity within the supply chain can have cascading effects, as well as impact several organizations downstream. Cybercriminals are exploiting these interdependencies, and they use vulnerabilities to gain unauthorized access to a network of interconnected businesses. 5. Emergence of Insider Threats External threats remain a significant concern, but the rise of insider threats is adding a layer of complexity. It's added to the already complex cybersecurity landscape. Insiders inadvertently contribute to data breaches. Whether through malicious intent or unwitting negligence, organizations are now grappling with a challenge. They need to distinguish between legitimate user activities and potential insider threats. 6. IoT Devices as Entry Points The proliferation of Internet of Things (IoT) devices has expanded the attack surface. There’s been an uptick in data breaches originating from compromised IoT devices. These connected endpoints range from smart home devices to industrial sensors and are often inadequately secured. This provides cyber criminals with entry points to exploit vulnerabilities within networks. 7. Critical Infrastructure in the Crosshairs Critical infrastructure has become a target of choice for cyber attackers. This includes energy grids, water supplies, and transportation systems. The potential consequences of a successful breach in these sectors are often financial. But that’s not all. They can also extend to public safety and national security. As cyber threats evolve, safeguarding critical infrastructure has become an urgent imperative. 8. The Role of Nation-State Actors Geopolitical tensions have spilled into the digital realm. Nation-state actors are increasingly playing a role in sophisticated cyber campaigns, and these actors are often driven by political motives. They use advanced techniques to compromise sensitive data and disrupt operations. This is to advance their strategic interests in the global cyber landscape. 9. The Need for a Paradigm Shift in Cybersecurity The surge in data breaches underscores the need to rethink cybersecurity strategies. It's no longer a question of if an organization will be targeted but when. Proactive measures include:
10. Collaboration and Information Sharing Collaboration among organizations and information sharing within the cybersecurity community are critical, especially as cyber threats become more sophisticated. Threat intelligence sharing enables a collective defense against common adversaries. This allows organizations to proactively fortify their defenses, and they do this based on insights gained from the broader cybersecurity landscape. Protect Your Business from Devastating Data Breaches The surge in data breaches in 2023 serves as a stark reminder. It reminds us of the evolving and pervasive nature of cyber threats and the urgent need for heightened cybersecurity awareness, robust defensive measures, and a commitment to adapt to the ever-changing tactics of cybercriminals. Need help protecting your business? Contact us today to schedule a chat: ContactUs@CyberProtex.com or 256-401-7072. Article used with permission from The Technology Press. You cannot overstate the importance of cybersecurity. Especially in an era dominated by digital advancements.
Businesses and organizations are increasingly reliant on technology to drive operations. This makes them more susceptible to cyber threats. 66% of small businesses are concerned about cybersecurity risk. Forty-seven percent lack the understanding to protect themselves. This leaves them vulnerable to the high cost of an attack. Conveying the tangible value of cybersecurity initiatives to decision-makers can be challenging. The need for protection is clear, but executives want hard data to back up spending. We’ll explore strategies to effectively show the concrete benefits of cybersecurity measures. These can help you make the case for stronger measures at your company, as well as help you understand how your investments return value. How to Show the Monetary Benefits of Cybersecurity Measures Why does demonstrating the monetary value of digital security measures pose a challenge? The benefits of cybersecurity are often indirect and preventive in nature. This differs from tangible assets with direct revenue-generating capabilities. Investments in robust cybersecurity protocols and technologies are akin to insurance policies. They aim to mitigate potential risks rather than generate immediate financial returns. Quantifying the exact monetary value of avoided breaches or data loss can be elusive. These potential costs are hypothetical. They're also contingent on the success of the cybersecurity measures in place. Additionally, success is often measured by incidents that do not occur. This complicates efforts to attribute a clear monetary value. As a result, companies grapple with finding certain metrics. Ones that effectively communicate this economic impact. Below are several ways to translate successful cybersecurity measures into tangible value. 1. Quantifying Risk Reduction What's one of the most compelling ways to showcase the value of cybersecurity? It's by quantifying the risk reduction. Companies design cybersecurity initiatives to mitigate potential threats. By analyzing historical data and threat intelligence, organizations can provide concrete evidence. Evidence of how these measures have reduced the likelihood and impact of incidents. 2. Measuring Incident Response Time The ability to respond swiftly to a cyber incident is crucial in minimizing damage. Metrics that highlight incident response time can serve as a key indicator. They can illustrate the effectiveness of cybersecurity efforts. It’s also possible to estimate downtime costs, then correlate those to a reduction in the time it takes to detect and respond to a security incident. This demonstrates potential savings based on faster response. The average cost of downtime according to Pingdom is as follows:
3. Financial Impact Analysis Cybersecurity incidents can have significant financial implications. Businesses can quantify the potential losses averted due to cybersecurity measures. Businesses do this by conducting a thorough financial impact analysis. This can include costs associated:
4. Monitoring Compliance Metrics Many industries have regulatory requirements for data protection and cybersecurity. Demonstrating compliance with these regulations avoids legal consequences. It also showcases a commitment to safeguarding sensitive information. Track and report on compliance metrics. This can be another tangible way to exhibit the value of cybersecurity initiatives. 5. Employee Training Effectiveness Human error remains a significant factor in cybersecurity incidents. Use metrics related to the effectiveness of employee training programs. This can shed light on how well the company has prepared its workforce. Prepared it to recognize and respond to potential threats. A well-trained workforce contributes directly to the company’s cybersecurity defenses. 6. User Awareness Metrics Beyond training effectiveness, there are user awareness metrics. These gauge how well employees understand and adhere to cybersecurity policies. Use metrics such as the number of reported phishing attempts. As well as password changes and adherence to security protocols. These metrics provide insights into the human element of cybersecurity. 7. Technology ROI Investing in advanced cybersecurity technologies is a common practice. Showcasing the return on investment (ROI) can be a powerful way to show value. Use metrics that assess the effectiveness of security technologies. Specifically, in preventing or mitigating incidents. Such as the number of blocked threats. This can highlight the tangible benefits. 8. Data Protection Metrics For organizations handling sensitive data, metrics related to data protection are paramount. This includes monitoring the number of data breaches prevented. As well as data loss incidents and the efficacy of encryption measures. Show a strong track record in protecting sensitive information. This adds tangible value to cybersecurity initiatives. 9. Vendor Risk Management Metrics Many organizations rely on third-party vendors for various services. Assessing and managing the cybersecurity risks associated with these vendors is crucial. Metrics related to vendor risk management showcase a comprehensive approach to cybersecurity, such as the number of security assessments conducted or improvements in vendor security postures. Schedule a Cybersecurity Assessment Today Demonstrating the tangible value of cybersecurity starts with an assessment. One that uncovers the status of your current security measures. Knowledge is power when fostering a culture of security and resilience! Contact us today to schedule a chat: 256-401-7072 or ContactUs@CyberProtex.com Article used with permission from The Technology Press. Technology is reshaping the world of work at an unprecedented pace. From artificial intelligence to web3, from the metaverse to the hybrid work model. We are witnessing a series of technological revolutions. They are transforming how we communicate, collaborate, create, and innovate.
Let’s explore some of the most impactful technology trends that are changing the way we work in 2024 and beyond. 1. Artificial Intelligence AI and Generative AI are not just buzzwords. They are transforming the workplace. These technologies enable automation, allowing teams to handle mundane tasks more efficiently. They free up human resources for more creative and strategic endeavors. AI is not a new concept, but it has become more powerful and accessible in recent years. This is thanks to advances in computing power, data availability, and algorithm development. Artificial intelligence is now augmenting and automating various aspects of work. This includes data analysis, customer service, image creation, product design, and more. But AI also poses significant challenges and risks. This includes ethical dilemmas, social implications, and workforce displacement. Thus, it's essential to adopt responsible and human-centric approaches to AI. As well as ensure that workers have the skills and support to adapt to the changing nature of work. 2. Remote Collaboration Tools Advanced collaboration tools have facilitated the rise of remote work. These include video conferencing, project management software, and cloud-based document sharing platforms. This technology empowers teams to collaborate seamlessly from different corners of the globe. These tools break down geographical barriers, allowing for efficient teamwork and real-time communication. The hybrid work model is a term that describes the combination of remote and in-office work. This is not a new concept, but it has become more prevalent in the wake of the Covid-19 pandemic. The hybrid work model offers many benefits, such as:
The hybrid work model is transforming the way we work. It requires workers to have new skills, tools, and strategies. For example, hybrid work requires workers to have several capabilities to work effectively. These include strong digital literacy, communication, collaboration, and self-management skills. 4. Web3: The Decentralized Internet Web3 is a term that refers to the next generation of the internet. An internet based on decentralized technologies, such as:
Web3 aims to create a more open, transparent, secure, and democratic internet. One where users have more control over their own data, identity, and digital assets. Web3 also enables new forms of collaboration and value creation. This includes:
Web3 is transforming the way we work. It's creating new business models, platforms, and communities. These are designed to be more inclusive, participatory, and innovative. Web3 has the potential to generate $49.10 billion in economic value by 2030. 5. Internet of Things (IoT) in the Workplace IoT devices are creating smart and optimized workplaces. This includes smart thermostats that adjust office temperatures based on occupancy. As well as wearable devices that track employees' health and productivity. This connectivity enhances efficiency and reduces energy consumption. It also provides valuable data for informed decision-making. 6. Augmented Reality (AR) and Virtual Reality (VR) AR and VR technologies are revolutionizing training, design, and customer interactions. In the workplace, AR and VR offer immersive training experiences. These allow employees to learn complex tasks in a simulated environment. These technologies are also used in product design. This enables professionals to visualize and modify prototypes in real time. This drives faster innovation cycles. 7. Cybersecurity Advancements As digital technologies advance so do cybersecurity threats. Businesses are investing in advanced cybersecurity measures to protect sensitive data. As well as ensuring the privacy of employees and customers. These innovations include biometric authentication and AI-driven threat detection. Cybersecurity advancements are crucial. They help companies safeguard digital assets and maintain trust in the online workspace. The Impact on the Future of Work These transformative technology trends are not just fleeting novelties. They are shaping the future of work. Businesses that adapt and embrace these technologies gain a competitive edge. Remote collaboration tools foster flexibility and work-life balance, appealing to the modern workforce. AI and automation enhance efficiency, reducing errors and operational costs. IoT creates intelligent workspaces, enhancing employee well-being and environmental sustainability. AR and VR drive innovation, offering new ways to engage both employees and customers. Challenges and Considerations While these technologies bring immense benefits, they also pose challenges. Workforce training is essential to ensure employees can leverage these tools effectively. Additionally, there are ethical considerations about data privacy and security. As well as the impact of automation on employment. Striking a balance between technological advancement and human welfare is crucial. Especially in this transformative era. Let Us Guide You Successfully Through Digital Transformation Navigating new technologies can be complex. There are pitfalls that can waste time and money. Avoid this by working with our team of experts. We can help you customize your transformation to fit your business goals. Give us a call today to schedule a chat: 256-401-7072. Article used with permission from The Technology Press. As we step into the new year, it's the perfect time to reflect on our digital habits and initiate a much-needed cleanup of our virtual spaces. In an era where our lives are intricately woven into the digital realm, CyberProtex is here to guide you through the process of decluttering your digital life in 2024.
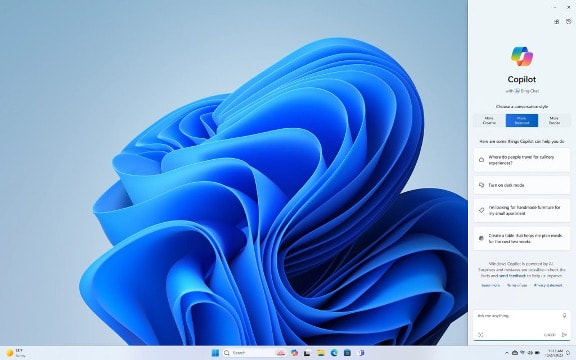
Let's pave the way for a secure and organized new year with ten simple ways to reduce digital clutter and enhance your overall cybersecurity posture: 1. Audit Your Digital Footprint Start by taking stock of your online presence. Review the accounts you've created over the years, from social media platforms to online shopping sites. Close any accounts you no longer use and update passwords for those you decide to keep. This helps minimize the potential attack surface for cybercriminals. 2. Secure Your Passwords Make 2024 the year you prioritize the security of your online accounts. Consider using a password manager to generate and store complex, unique passwords for each of your accounts. Update passwords for critical accounts, such as email and banking, and enable two-factor authentication whenever possible. 3. Organize Your Files A cluttered digital space can slow you down and make finding important files a daunting task. Take the time to organize your files into folders with clear naming conventions. Consider using cloud storage solutions to keep your documents accessible and synchronized across devices, and regularly back up your important files to protect against data loss in the event of a cyber incident. 4. Review App Permissions Applications often request access to sensitive information. Periodically review the permissions granted to each app on your devices and revoke access to unnecessary data. This simple step enhances your privacy and reduces the risk of data breaches. 5. Clean Up Your Email Your email inbox can quickly become a chaotic mix of newsletters, promotions, and important communications. Unsubscribe from newsletters you no longer find valuable, create filters to organize incoming emails, and regularly delete unnecessary emails to keep your inbox streamlined. Be wary of unsolicited emails and avoid clicking on suspicious links. A tidy inbox not only improves efficiency but also reduces the risk of falling victim to phishing attacks. 6. Update Software and Devices Outdated software can pose security risks. Ensure that your operating system, antivirus software, and applications are up to date with the latest security patches. Regular updates help protect your devices from potential vulnerabilities. 7. Review Privacy Settings: Take the time to review and adjust privacy settings on your social media accounts and other online platforms. Limit the information visible to the public and ensure that you are comfortable with the level of access granted to third-party apps. 8. Educate Yourself on Phishing Threats Phishing attacks are becoming more common and increasingly sophisticated. Learn how to recognize phishing attempts, and be cautious when clicking on links or providing personal information online. CyberProtex recommends regular cybersecurity awareness training to stay informed about the latest threats. 9. Secure Your Smart Devices With the rise of smart devices, securing your digital life extends beyond traditional computers and smartphones. Change default passwords on smart devices, update firmware regularly, and review and adjust privacy settings to maintain control over the data collected by these devices. 10. Educate Yourself on Cybersecurity Best Practices The digital landscape is constantly evolving. Stay informed about the latest cybersecurity trends and threats. Follow reputable sources for cybersecurity news, and consider consulting with CyberProtex to ensure your digital defenses are up-to-date. By following these ten steps, you can declutter your digital life and start 2024 with enhanced cybersecurity. CyberProtex is committed to helping you navigate the ever-changing landscape of online threats. Contact us at 256-401-7072 or ContactUs@CyberProtex.com to access the tools and knowledge needed to navigate the digital world safely. Cheers to a clutter-free and secure 2024! In a world where technology constantly evolves, Microsoft stands at the forefront. It continues to pioneer innovations. Innovations that transform how we interact with our digital universe. The fall Windows 11 update is a testament to Microsoft's commitment to excellence. It’s more than just an upgrade. It's a leap into the future of computing. Microsoft touts it as “The most personal Windows 11 experience.” Let’s explore some of the great features that make this update so significant. Microsoft Copilot: Your Intelligent Partner in Creativity A standout feature of the fall Windows 11 update is Microsoft Copilot. This AI-driven marvel is like your personal PC assistant. Need help summarizing a web page? Want to change to dark mode, but forgot how? Looking for a quick custom image for a social media post? Microsoft Copilot can do all that and more. Image credit: Microsoft Copilot is seamlessly integrated into Windows 11. It offers real-time suggestions and turns ideas into reality with remarkable ease. Ask it what you need, and the AI engine gets to work.
Updated Apps (Paint, Snipping Tool, Clipchamp & More) Have you ever wished that Windows’ Snipping Tool could do more? This update grants that wish. The Snipping Tool is just one of many to get an AI upgrade. Look for new capabilities in Paint, Clipchamp, and Photos. Get a unique image from inputting a text prompt and style. The Cocreator tool in Paint makes it easy to jumpstart your creativity. It will generate the image, then you can edit it in the same app. Microsoft Clipchamp is one of the easiest video creator tools out there. You can now just drag in your assets and clips. Then, click to have the AI engine work its magic to create a video for you. The new Clipchamp Auto Compose feature can: • Recommend scenes • Make edits • Create a narrative based on your inputs Easy Data Migration with Windows Backup When you buy a new computer, moving data can be a pain. It can take hours to move your “pc life” between devices. And there’s always the risk you’ll miss something. The new Windows Backup feature makes moving between computers easier. You can choose backup options and folders. When ready to move, it’s a simple process. You can restore the new PC from another backed-up PC. Microsoft Edge: A Faster and More Secure Browsing Experience Microsoft Edge received significant enhancements. These focus on speed, responsiveness, and security. The Edge Secure Network feature offers more gigabytes. Microsoft increased user storage from 1GB to 5GB. This function encrypts your internet connection to secure data. Edge Secure Network has many features of a VPN. This is great for extra online security. It’s also helpful for companies trying to prevent breaches from clicks on phishing links. Save Energy & Battery Power A feature called Adaptive Dimming is another enhancement of this update. Your screen slowly dims if you’re no longer paying attention. This has the dual benefit of saving energy and helping you refocus. PC sensors power this feature as well as two others. So, it’s going to be more common with newer computers. The other two features that use sensors are: • Wake on Approach • Lock on Leave A More Personal Windows 11 Experience Beyond the technical innovations, this update brings more. Including a more personal touch to the user experience. Tailored to individual preferences, Windows 11 becomes an extension of the user's identity. This includes things like: • Personalized themes • Custom widgets • Intelligent assistants Every interaction feels curated and intuitive. It makes for a truly personalized operating system. Other Cool Enhancements There’s a lot of excitement packed into Windows 11. Here are a few more new features you can explore. • Copilot in Microsoft Shopping: Find what you need fast when shopping online. Bing will provide tailored recommendations based on your requests. • Content Credentials: Add an invisible digital watermark to your AI-generated images in Bing. Cryptographic methods help you tag your work. • Bing Chat Enterprise Updates: Boost work creativity and enjoy multimodal visual search. Find information using only images. • DALL.E 3 Model from Open AI: Use the Image Creator in Bing and you’ll likely be impressed. It’s had an upgrade and uses the DALL.E 3 model to render images from text prompts. Harness the Power of Microsoft Products Microsoft is definitely a leader in work productivity tools. And it has been for a long time. If you’re still working like it was 2020, let us help you upgrade. Employees can be more efficient than ever with the right apps. As a trusted Microsoft Gold Partner, we’ve got your back with Microsoft 365, Windows 11, and other solutions. Our experts will guide you, so you can gain an edge on the competition. Give us a call today at 256-401-7072 or email ContactUs@CyberProtex.com to schedule a chat. Article used with permission from The Technology Press. As the holiday season approaches, the excitement of Black Friday and Cyber Monday shopping takes center stage. While you're busy hunting for the best deals and discounts, it's crucial to keep your cybersecurity in check. In the age of digital transactions and online shopping, protecting your personal and financial information is more important than ever. This Thanksgiving, CyberProtex is here to ensure you have a safe and secure shopping experience.
Follow our five top tips to navigate the upcoming online shopping frenzy with confidence. 1. Update and Secure Your Devices: Before diving into the world of holiday shopping, make sure all your devices are up to date with the latest security patches and updates. This includes your computer, smartphone, and any other gadgets you'll be using to find the best deals. Enable automatic updates to ensure you have the latest security features, protecting you from potential vulnerabilities. 2. Shop Only on Secure Websites: Stick to reputable and well-known online retailers to minimize the risk of falling victim to cyber threats. Look for the "https://" in the website URL, indicating a secure connection. Avoid making purchases on websites that lack this crucial security feature. CyberProtex recommends double-checking the site's legitimacy by reading reviews and checking for trust seals before entering any personal information. 3. Use Strong and Unique Passwords: A strong password is your first line of defense against cyber threats. Create unique passwords for each online store you visit, combining a mix of uppercase and lowercase letters, numbers, and special characters. If managing multiple passwords seems overwhelming, consider using a trusted password manager to securely store and generate complex passwords for you. 4. Enable Two-Factor Authentication (2FA): Adding an extra layer of security to your online accounts, especially those containing sensitive information, is crucial. Enable two-factor authentication whenever possible. This typically involves receiving a code on your mobile device or email that you'll need to enter along with your password, providing an additional barrier against unauthorized access. 5. Monitor Your Accounts Regularly: Keep a close eye on your bank and credit card statements during the holiday season. Regularly check for any suspicious transactions or unfamiliar charges. The sooner you spot and report any unauthorized activity, the quicker you can resolve the issue and minimize potential damage. This Thanksgiving, as you embark on your Black Friday and Cyber Monday shopping adventures, make cybersecurity a top priority. By following these tips, you can navigate the online marketplace with confidence, knowing that your personal and financial information is secure. From all of us at CyberProtex, we wish you a happy and cyber-safe holiday season! |